In our conversations with clients and prospects, we often learn that finance leaders and founders/CEOs feel overwhelmed by cyber security compliance requirements: there are certifications, regulations, insurance questions, technical tools, and a steady stream of headlines telling you the risks are rising.
This article aims to simply cyber security and enable you to understand what good looks like and how to take the sensible next steps.
Tier 1: Front‑line security: stop the most common attacks
The basics: this step is about protecting your business from the most common cyber attacks. Think of it as locking the doors and windows.
In the UK, this tier is best represented by Cyber Essentials, the government‑backed baseline for cyber security . Cyber Essentials focuses on five core areas that prevent the majority of commodity attacks:
-
Firewalls and secure network boundaries
-
Secure configuration of devices and systems
-
Controlled user access (including admin rights)
-
Malware protection on all endpoints
-
Timely security updates and patching
These controls won’t stop every attack, but they are proven to block the most common ones. That’s why Cyber Essentials is increasingly required by customers, partners, and government bodies in supply chains.
What this means for your business:
-
It significantly reduces your exposure to everyday cyber risk
-
It provides a recognised, external signal that you take security seriously
-
It is often a prerequisite for winning contracts or even being considered as a supplier
Tier 2: Managing impact: insurance, regulation, and response
Tier two accepts a hard truth: no organisation is immune. Even with good front‑line controls, incidents can and will happen. This tier looks beyond prevention and focuses on how you manage risk, respond to incidents, and protect sensitive information.
It is driven by two forces:
1. Cyber liability insurance
2. Industry and regulatory requirements (for example NHS, government supply chains, financial services)
Cyber insurers are no longer satisfied with a checklist of technology or software that your business has bought. They want confidence that, if something goes wrong, you can detect it quickly and respond effectively.
Common insurer expectations include:
-
A documented incident response plan
-
Evidence of 24/7 monitoring and rapid escalation
-
Managed Detection and Response (MDR), not just antivirus
-
Regular risk assessments and staff awareness
Insurers increasingly look for specialist response capability, not just proof that software is installed.
Simply put, insurers care less about whether malware exists on a device, and more about how quickly you know, who responds, and how damage is contained.
Regulation focuses on data and accountability
If you operate in regulated sectors or handle sensitive data, Tier 2 becomes unavoidable.
Regulators and industry frameworks tend to focus on:
-
Protection of confidential and personal data
-
Clear ownership and accountability
-
Incident response and reporting
-
Ongoing risk management
This is where cyber security isn’t primarily an “IT problem” and becomes a business priority.
Tier 3: Security standards: proving maturity and future readiness
Tier 3 looks at the whole organisation. It asks a broader question: Is security embedded into how the business operates, today and in the future?
This tier is represented by recognised standards such as ISO 27001, which assesses people, process, and technology together.
Unlike Cyber Essentials, standards don’t prescribe specific tools. Instead, they assess whether you:
-
Understand your information risks
-
Have clear policies and governance
-
Can evidence how security is applied in practice
-
Review, test, and improve over time
ISO 27001, for example, is built around an Information Security Management System (ISMS) that emphasises risk‑based decision‑making and continuous improvement.
This tier matters when:
-
Customers ask deeper security questions during procurement
-
You operate internationally or in highly regulated markets
-
You want long‑term confidence, not just point‑in‑time compliance
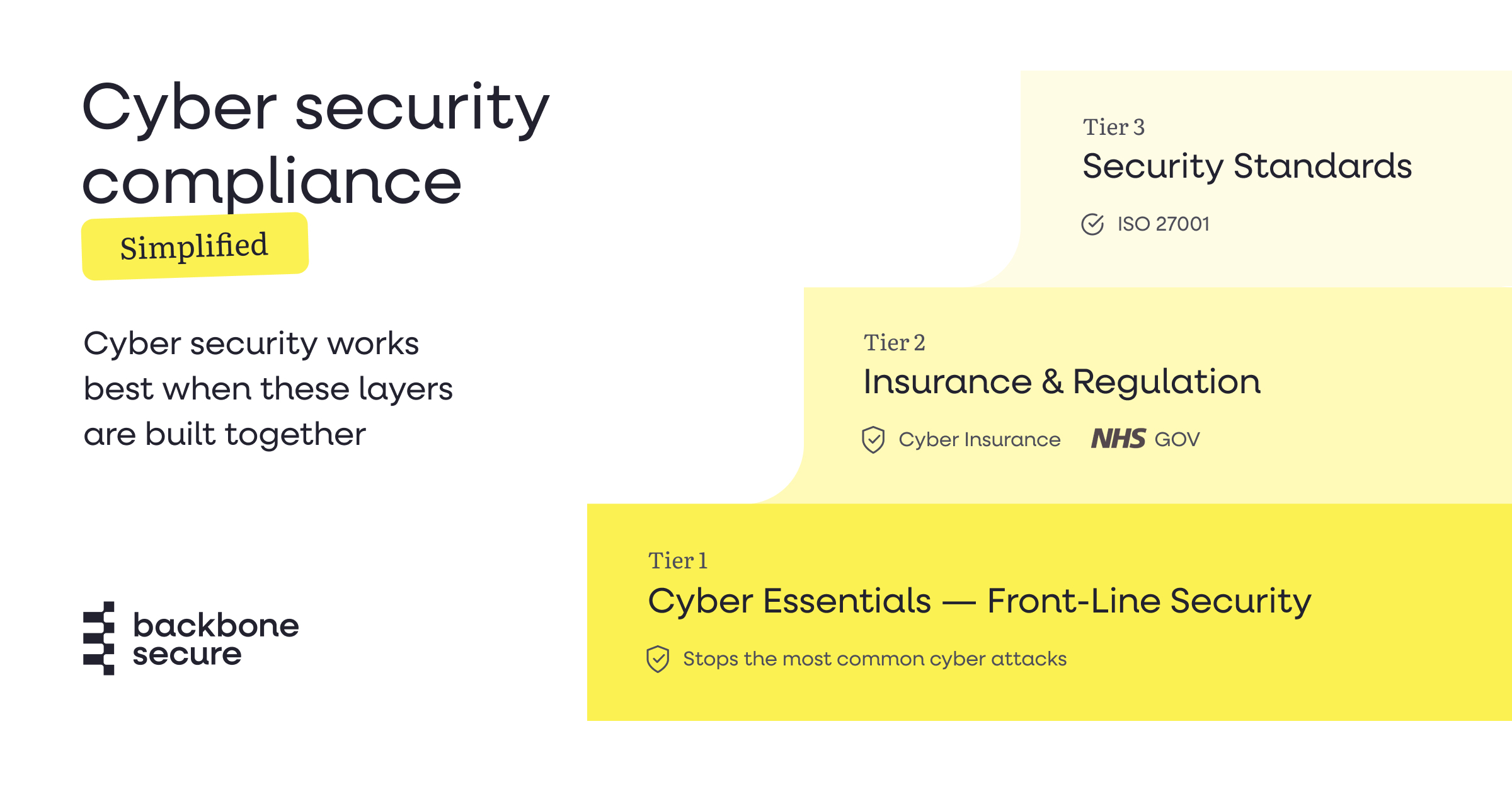
How the three tiers work together
These tiers are not alternatives, they are stacked.
-
Tier 1 protects you from common attacks
-
Tier 2 reduces impact and financial exposure when incidents occur
-
Tier 3 demonstrates maturity, governance, and future readiness
A common mistake we see is jumping straight to Tier 3 without solid Tier 1 foundations, or treating Cyber Essentials as “the end”. In reality, Cyber Essentials is the starting point.
Why this matters right now for UK businesses
We’re seeing increased interest in Cyber Essentials across UK supply chains. Customers are being asked to prove their security, or else be excluded from procurement processes.
By understanding these three tiers, you can:
-
Make better investment decisions
-
Speak confidently to customers, insurers, and partners
-
Show that your organisation plays its part in a collective defence
Cyber security is no longer just about protecting your own business. It’s about protecting the ecosystem you operate in.
If you’re early in this journey, start with Tier 1 and build forward deliberately. If you already have Cyber Essentials, use it as a platform to strengthen your incident response and data protection capabilities.
Security doesn’t need to be complicated, but it does need to be intentional.
If you’d like help mapping where your organisation sits across these three tiers, we're happy to have a conversation.



